Anyone who knows me will tell you I’m a car guy. And any car guy (as opposed to a Porsche guy or a Corvette guy or a Miata guy) will tell you that every car guy ought to have owned an Alfa Romeo. The problem is that in order to have owned an Alfa Romeo, you must first own an Alfa Romeo; and then, presumably, either you get rid of it or it gets rid of you, or you both get rid of each other. And until today, I had not yet owned an Alfa Romeo.
This afternoon, I graduated from “has not yet owned an Alfa Romeo” to “currently owns an Alfa Romeo”. Specifically, a 2007 Alfa Romeo 147 1.6 TS. At some point in the future, I will move on from “currently owns an Alfa Romeo” to “has owned an Alfa Romeo”, thereby completing my car guy journey; but that will take a lot of work and a bit of money, although in theory I should be able to flip it for a decent profit.
Yes, it’s red, and yes, it has little Italian flags all over.
Currently planned work:
- Install “24h Le Mans” sticker on trunk lid for immediate 5 bhp boost
- Change all fluids and filters
- Replace rear wiper blade
- Polish headlights
- Investigate lifter tick
- Replace clutch pump and / or follower and / or hydraulic line
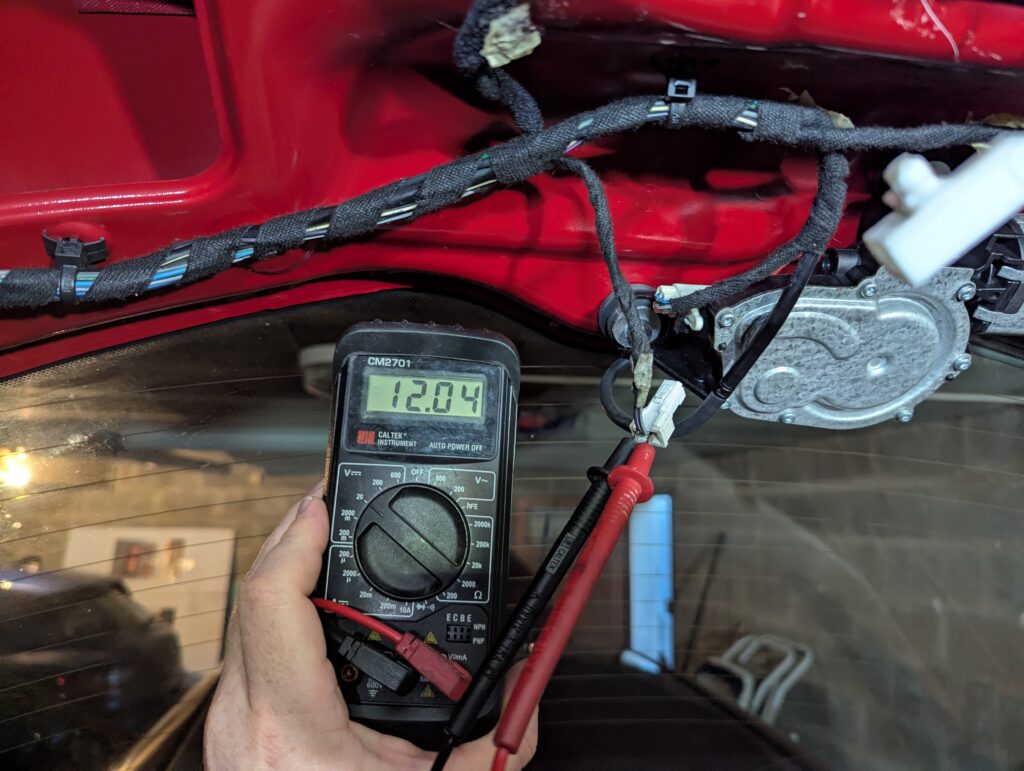
- Replace passenger side window regulator
- Replace driver side window and mirror controls
- Replace trunk lid lock actuator
- Fix driver’s seat release
- Fix or replace various bits of interior trim
- Replace gear shift lever knob, possibly with a shorter one
- Replace whip antenna with either bee sting or shark fin
Maybe I’ll even remember to post updates.
Update: 5 bhp boost unlocked

Update: of course my Italian car has electrical gremlins.
Update 2026-03-16: I had low washer nozzle pressure and assumed the pump might need changing. Only after ordering a replacement pump from a breaker did I realize that the real issue was that the washer hose was getting pinched when I closed the hood. Cutting the cable ties that tied it to the hood strut solved the issue.

Update 2026-03-19: It passed inspection today, with a slew of minor defects but little I wasn’t already aware of and nothing I can’t fix.